| weo | Date: Saturday, 2012-01-07, 7:33 PM | Message # 1 |
|
Colonel
Group: Moderators
Messages: 151
Status: Offline
| 1. Do not use WEP
WEP (wired equivalent privacy) has long been dead. Its encryption capabilities can be easily and quickly broken by most non-professional hacker. Therefore, you should not use WEP at all. If you are using, please upgrade immediately to WPA2 (Wi-Fi protected access) with 802.1X authentication. If you are new to a wifi router or access point does not support WPA2, try a simple firmware update or new equipment is replaced.
2. Do not use WPA/WPA2-PSK
Pre-shared key mode (PSK) of the WPA and WPA2 are not secure for enterprise environment very much. When using this mode, need to fill key for each transmitter PSK wifi. Therefore, this key should be changed each time an employee leaves the company and when a transmitter is lost or stolen - things have not really been focusing most corporate environments.
3. Implement 802.11i
Mode EAP (extensible authentication protocol) security of WPA and WPA2 use 802.1X authentication PSKs instead, providing the ability to give each user or device a separate login information: username and password password or a certificate electronically.
The actual encryption key will be changed regularly and exchange "silently" in background. Therefore, if you want to change or a change in personnel, everything you need to do is adjust the login at the server focus, instead of changing the PSK in each device. Key PSK also prevent users from eavesdropping network traffic of another - a very easy to do with the add-on tools such as Mozilla Firefox or Firesheep DroidSheep application for Google Android.

Keep in mind that, to obtain the highest possible security, you should use WPA2 with 802.1X, or 802.11i.
To enable 802.1X authentication, you need to have a server RADIUS / AAA. If you are running Windows Server 2008 or higher, consider using Network Policy Server (NPS) or Internet Authenticate Service (IAS) (or earlier server versions). If you are not running Windows Server, you can use open source FreeRADIUS server.
You can apply settings for 802.1X devices via Group Policy if you are running Windows Server 2008 R2. If not, try to consider using a 3rd party solution to any device configuration.
4. Implementing 802.1X security settings
EPA WPA/WPA2 mode is capable of being attacked by the part-time hacker. However, you can block them from attack by EAP security settings for the device. For example, the EAP settings for Windows, you can enable the authentication server confirmation by selecting the CA certificate, server address assignment and disable it from asking users to trust the new server authentication or CA.
You can apply settings for 802.1X devices via Group Policy or using third party solutions, such as the Avenda Quick1X.
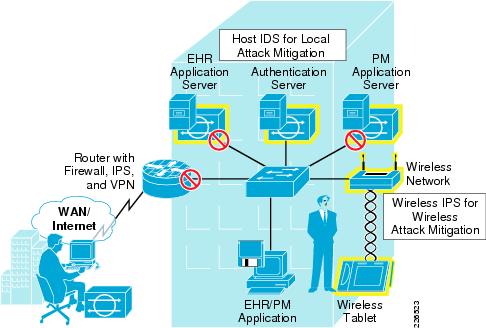
5. Should use a system to prevent unauthorized access to wireless network
Wireless network security is to do instead of focusing on trying to defeat those who gain access to your network. For example, the hacker can set up a virtual access point or perform DOS attacks - denial-of-service. To be able to detect and defeat these attacks so, you should deploy an intrusion prevention system Wireless (WIPS). Design and methods used in the WIPS differ according to each manufacturer, but generally they can monitor the network, notify the user and can prevent virtual access points or malicious activities.
|
| |
|
|